Call a Specialist Today! 888-785-4402 | Free Shipping!
Cisco Secure WAF and Bot Protection
Improve application availability and security with Cisco AppSec and bot protection solutions
Note: For our full product catalog, please visit our Cisco Security focused site at SecureCloudGuard.com.

Overview:
In today’s economy, your digital business must be secure and available … all the time. But your network and applications are under constant attack, making it difficult to ensure that data is secure and online revenues are protected.
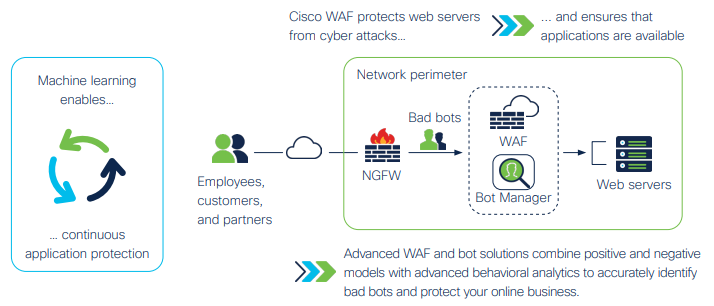
Cisco Secure Web Application Firewall (WAF) and bot protection defends your online presence and ensures that website, mobile applications, and APIs are secure, protected, and “always on.”
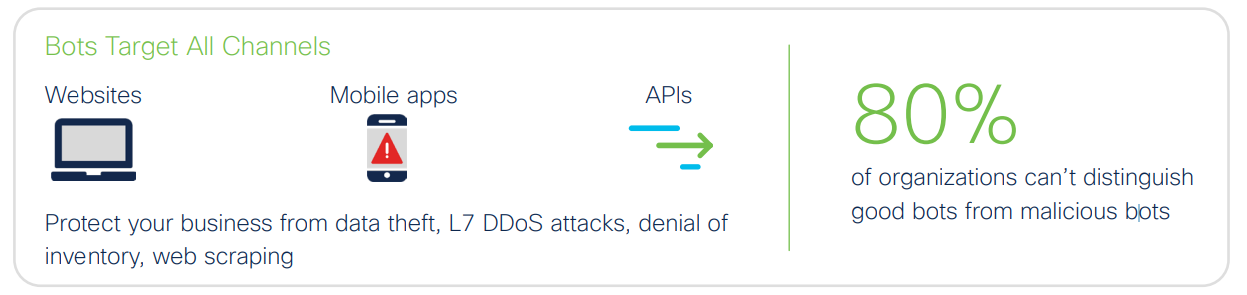
Advanced WAF and bot management solutions ensure reliable, secure delivery of web and mobile applications while minimizing costs by enabling security policies to easily be deployed across multicloud environments. Advanced bot management uses machine learning and adaptive security to accurately distinguish good bots from malicious bots, ensuring that your network and applications are available to legitimate users.
With business moving online and to the cloud, advanced WAF and bot solutions protect websites, applications, and APIs from attack and ensures that your organization is open for business.
Pricing Notes:
- Pricing and product availability subject to change without notice.